Product Hunt doesn't really work, but you should still use it to launch your product
Many of us have been launching on Product Hunt for a while, and more and more folks have started questioning whether the audience there is genuine and whether it is still worth launching on their platform.
Being fresh out of our latest launch from a week ago, I wanted to share here our first-hand experience and cover three main things:
- How does launching on Product Hunt look and feel today
- What we got from the launch
- How to make (the best) use of Product Hunt for your product
About us - launched 6x, >2,000 upvotes
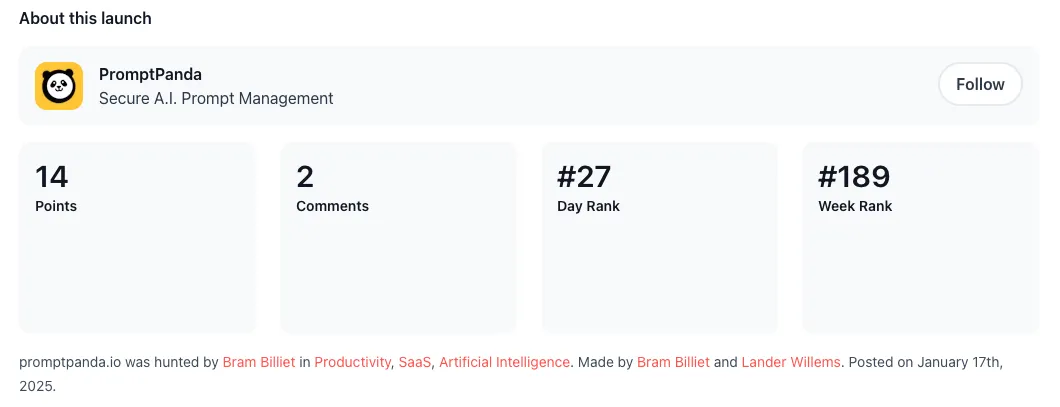
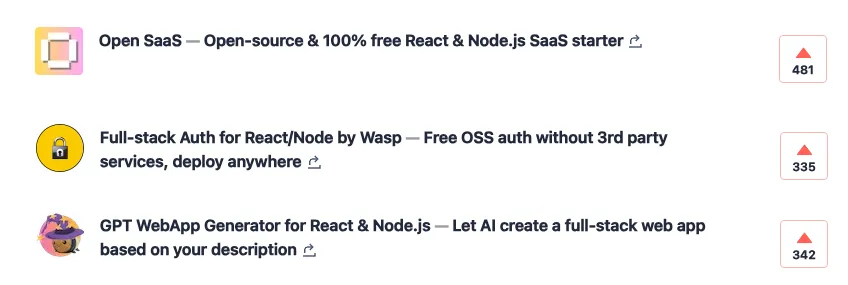
We’ve launched 6 times on Product Hunt in the last 4 years, won “Top Product” awards (#1 and #5 of the day), and collected over 2,000 upvotes in total. Our last launch was with Open SaaS - an open-source alternative to $300+ SaaS starters.
You will find many articles with advice for launching on PH, and winning stories from those who got featured, but almost nobody shares behind-the-scenes knowledge and what it really took to get there. That is the purpose of this post.
I will guide you through the steps of the launch and comment and share our experiences from each of them. Let’s get started:
Scheduling your launch and creating a “Coming soon” teaser - “let’s exchange upvotes”
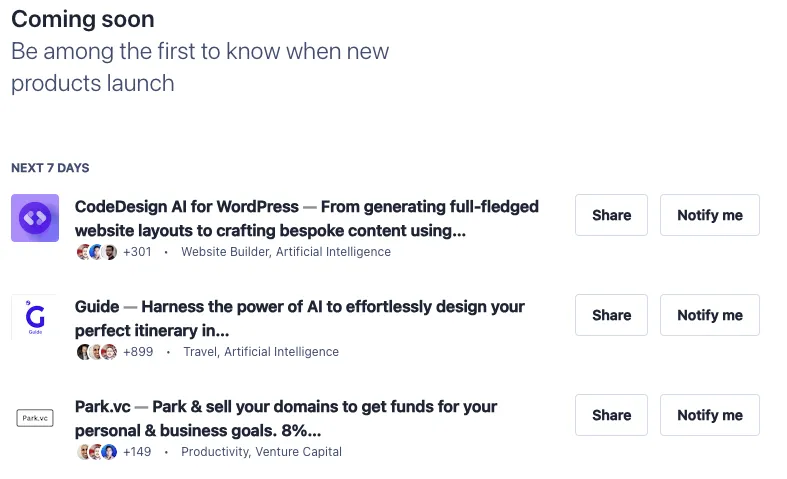
Once you schedule your Product Hunt launch, you can create a banner to appear on their “Coming soon” page (https://www.producthunt.com/coming-soon), and this is where your journey starts. This gives PH visitors an opportunity to see what’s coming next and to subscribe to get notified once it launches, and it is also the first thing you can use for marketing your launch.
This is also when the PH economy starts - as soon as you publish your launch teaser, you will start receiving offers to exchange upvotes with other people launching their products soon:
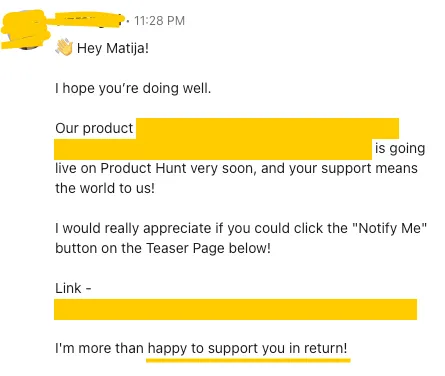
This is actually a legitimate strategy (in the sense of shared incentives and not buying votes) that can probably be utilized pretty efficiently via automation. It won’t bring any qualified leads (aka people genuinely interested in your product), but it might help with the upvotes, resulting in the increased visibility and reach of your launch.
We haven’t used this strategy at all (so I cannot testify to its efficiency), since we published our “Coming soon” page quite late, just a day or two before the launch, and we also didn’t have the workflow in place nor manpower to pull it off.
There are also specialized groups on Linkedin, WhatsApp, and other platforms for PH participants to support each other in this way. If you join these, you will, expectedly so, receive even more such messages and requests.
Launch day - unsolicited emails and “buy upvotes” offers
On the launch day, the requests like the one above intensified. I even got several emails from others launching products on the same day asking for an upvote, as they scraped my email and added me to their newsletter.
First 4 hours of the day - hidden upvotes
Product Hunt recently introduced the feature of showing the products in the randomized order, with the upvote count hidden, for the first 4 hours of the day. The idea behind this is to guarantee all products have equal visibility at the start and a fair chance to grab the attention of the audience.
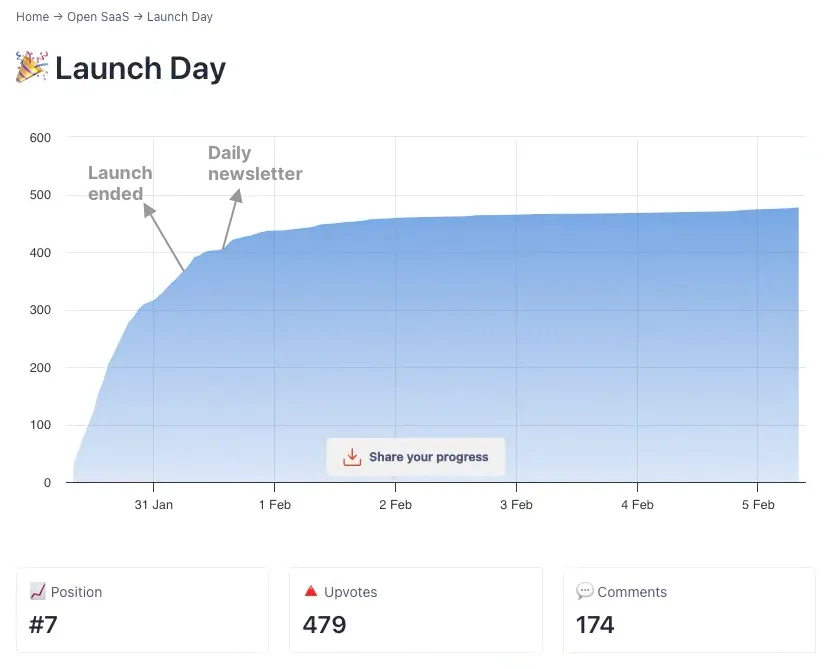
With our latest launch, Open SaaS, we had the best opening ever - 100 upvotes in 4 hours!

We, of course, engaged our network, but also noticed a lot of upvotes and comments from the people we don’t personally know. With such a strong start, I was quite confident we secured our place in the top 5 products on the leaderboard.
Being in the top 5 products is an “above the fold” position on Product Hunt’s home page, so getting there early is the best way to end up there.
But when the leaderboard was finally revealed, Open SaaS was barely in the top 10 launches of the day!

There was a quite noticeable cut-off between the first five places and the rest, and the product in the first place had almost double the upvotes than the second one. That was fairly demotivating for us as it felt like we had literally zero chance of catching up.
”Hey, wanna buy some upvotes?”
After the leaderboard reveal, we started receiving another type of message - direct offers to buy upvotes. Being still relatively close to being in the top 5 products probably made us a highly qualified lead:
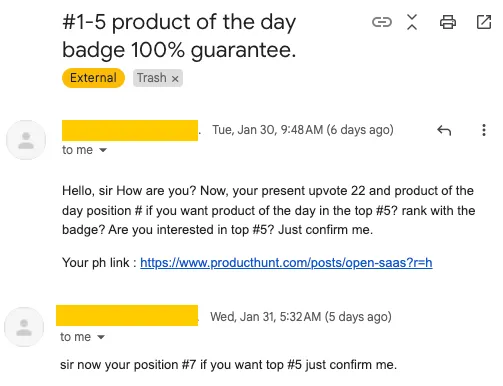
A slight variation of this is having different social media influencers and community owners reach out and offer to market your launch to their followers, promising X upvotes:
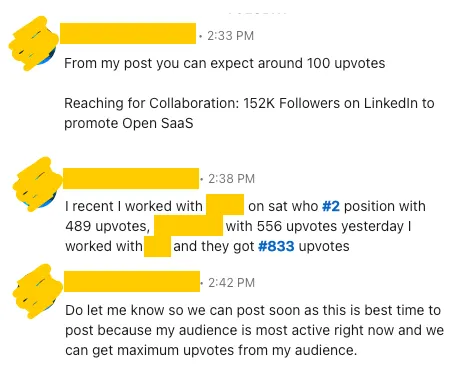
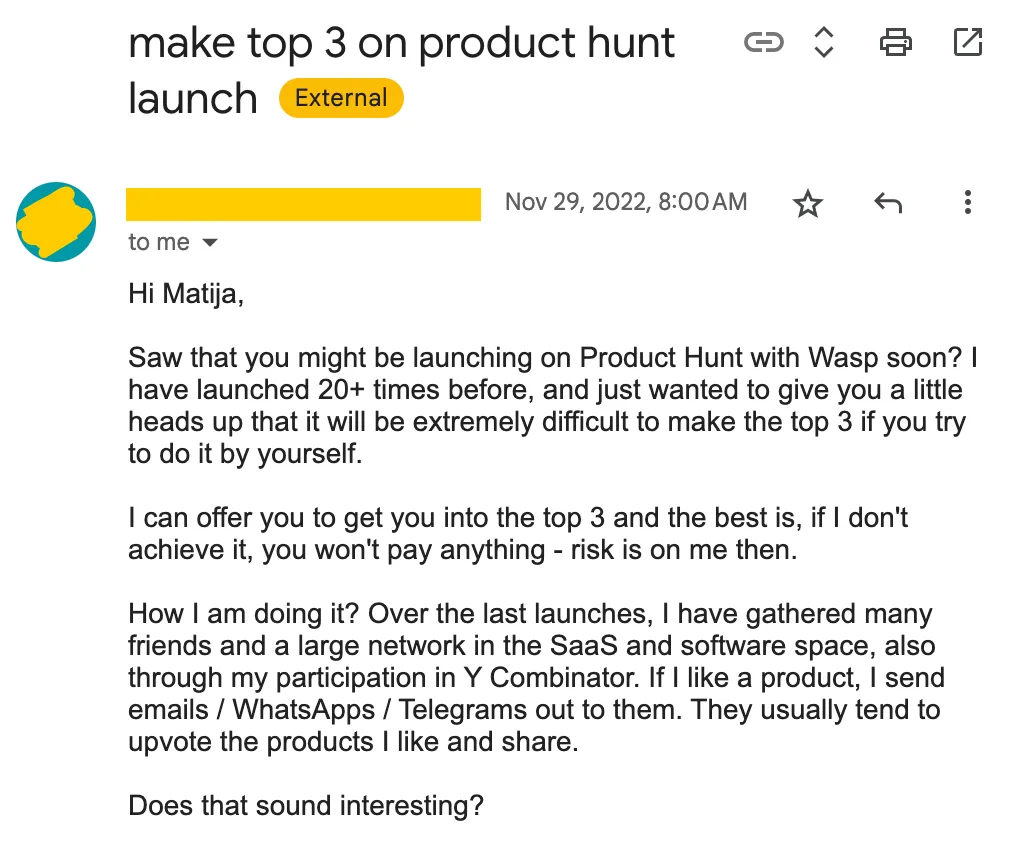
Even some of our direct contacts knew “a guy” that could get you to the top of Product Hunt and offered to intro us, so it kinda started feeling like a “public secret”, and us being the rare ones who didn’t know about it.
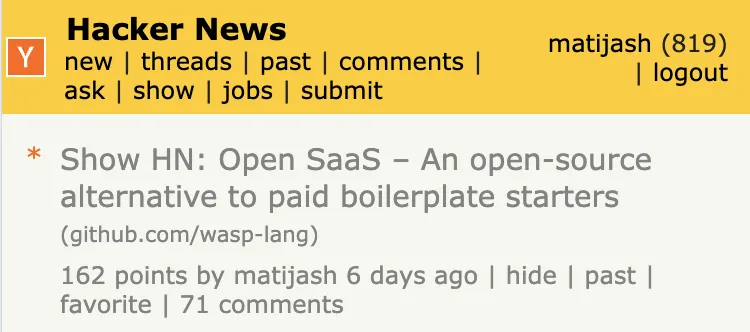
What we got from the launch - #7, HN front page, trending on GitHub, …
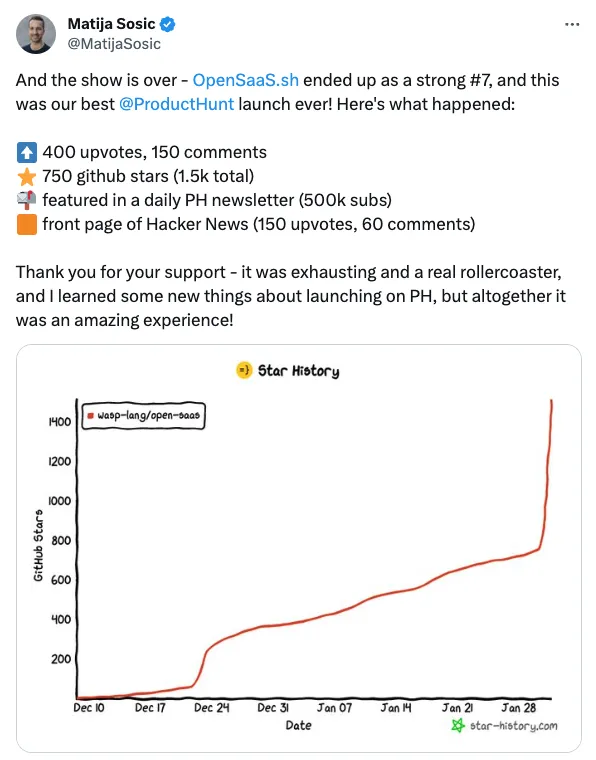
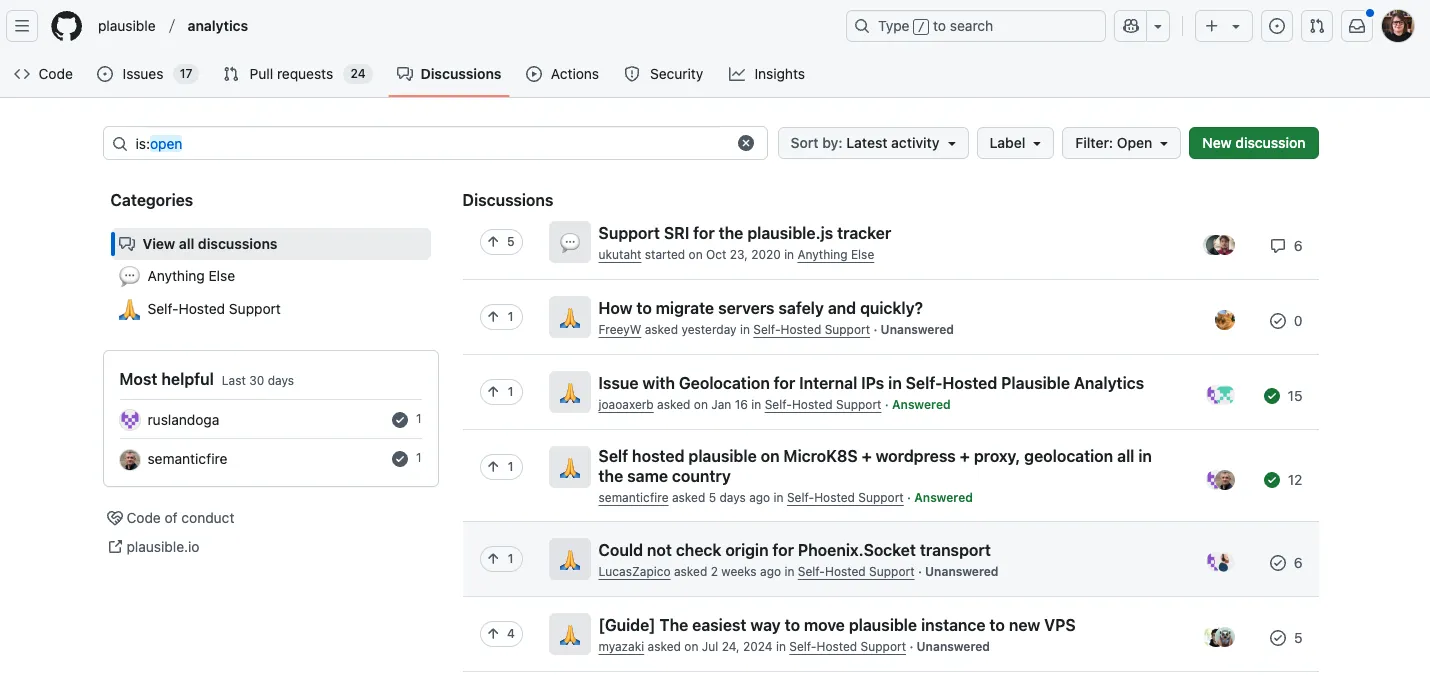
The main benefit of our PH launch wasn’t the launch itself, but rather the fact we could combine it with other things, like launching Open SaaS on HackerNews, where it ended up being featured for about half a day (and much longer on Show HN tab).
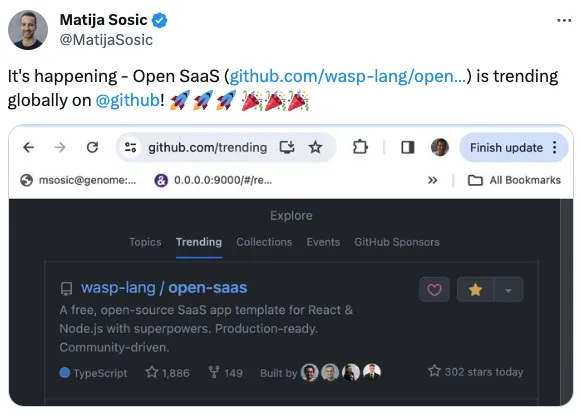
Finally, all that engagement combined allowed us to get trending globally on GitHub, which in turn brought in even more traffic to Open SaaS (today, a week after launching, it has over 2.5k stars).
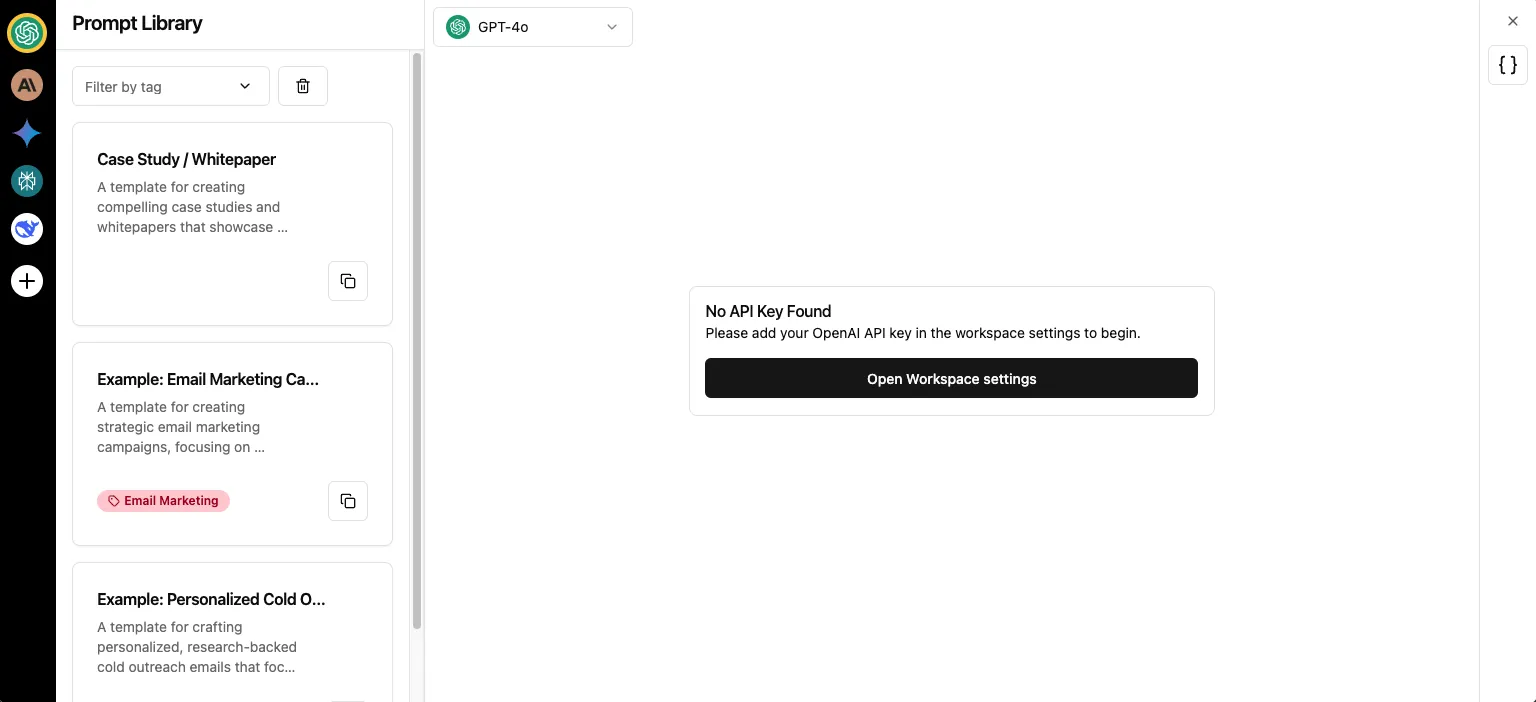
The resulting traffic
Taking a look at the traffic that was brought to Open SaaS’s repo in the last two weeks, here’s what we can observe:
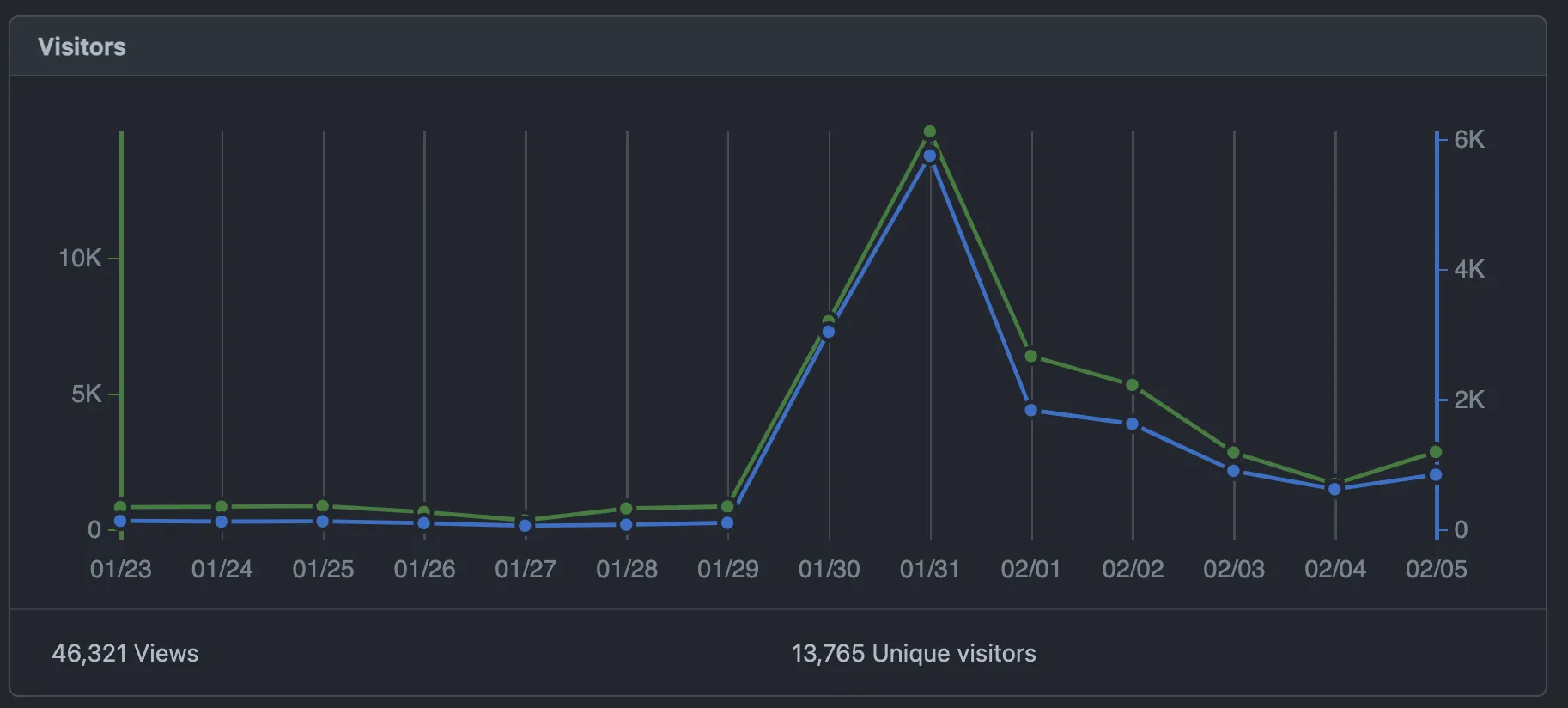
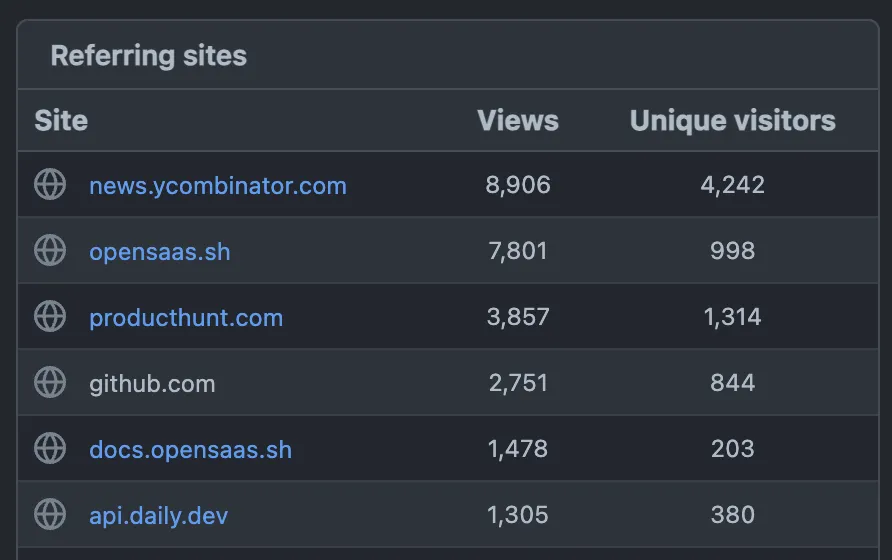
HackerNews launch brought in more than 3 times more people than Product Hunt. GitHub brought even fewer people to the actual repo, but my gut feeling is that many more of them starred it without leaving the Trending page.
Getting featured in PH’s daily newsletter - does it help?
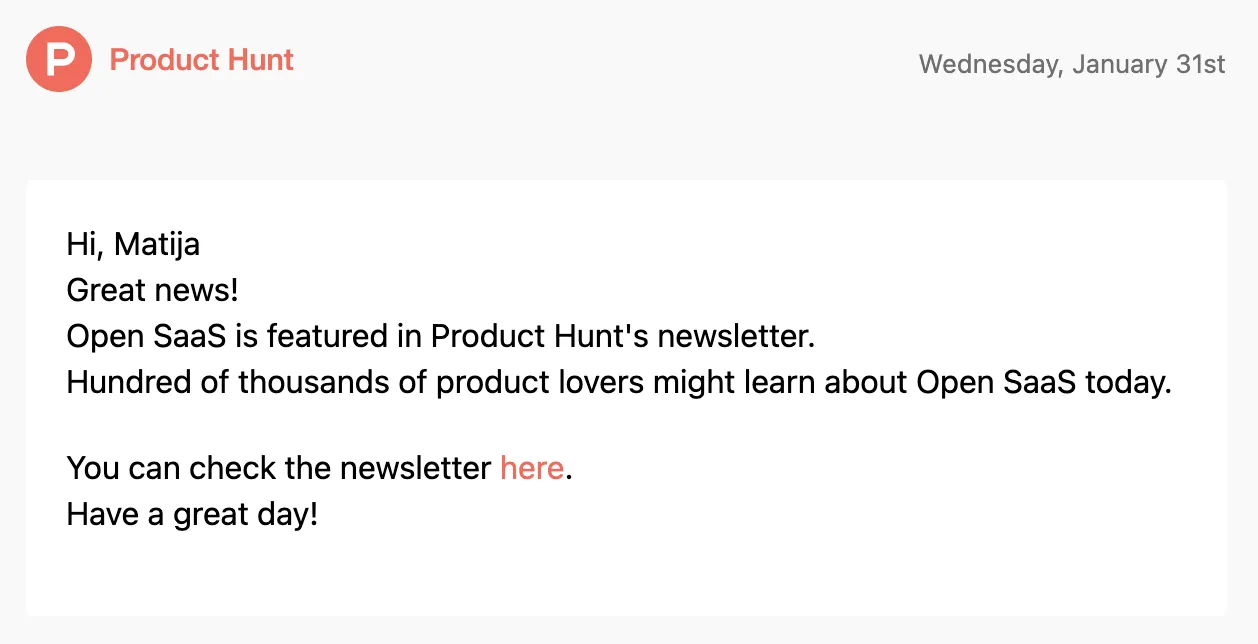
Open SaaS ended the launch as the #7 product of the day, with about ~400 upvotes. The top 10 products of the day end up in a daily newsletter that has over 500,000 subscribers, according to the Product Hunt.
The newsletter starts with 3 big promotional blocks, so you must scroll quite a bit to reach the top products of the previous day.
For us, it didn’t make a huge dent, I think it got us about 20 upvotes. Maybe it was due to the fact we weren’t number one, or simply because it’s quite a deep funnel (open email → scroll all the way down → check all the products → like Open SaaS → decide to upvote it).
Is it even possible to win #1 of the day without any boosting strategies?
Yes, it is definitely still possible. I’ve had it confirmed by a couple of contacts that I trust and who won #1 with their products, without any bots or paying for upvotes. But it’s also definitely become less common and less predictable.
Most of the times we were launching, the product in the first place exhibited some unusual behavior. Once, it was the company that launched the week before, but they just slightly rebranded the product and the website and re-launched it. Another time, a product received a very sudden spike in upvotes just hours before the end of the launch.
So, what does all this mean? Is it still worth launching on Product Hunt?
It is obvious that today, there are different forces and incentives driving the behavior of Product Hunt users from both sides. Initially, there was a community that wanted to learn about the latest products and express their interest, and there were founders that wanted to connect to that community.
Now, there are also creators who foremost want their product to win, no matter the actual audience engagement, as they believe that will help them with their end goal - e.g., reach, fundraising, or social validation towards other users. And there is obviously a side willing to fulfill that demand without having any real interest in the product.
Why is that possible? Product Hunt is taking a lot of measures to detect and prevent such behavior, but it is hard to do it without severely limiting the network effect (aka being able to share your launch link around) that Product Hunt is going for.
Besides all that, for us it is still worth it to regularly launch on Product Hunt. Here’s why.
Product Hunt is an amazing excuse
Product Hunt gives you a unique opportunity to declare an “official” launch of your product. You can decide on which day you want to do it, schedule it, and it’s 100% going to be there for everybody to see, and for you to share and invite people to check it out. You get 24 hours, during which it is fully justifiable to contact everyone you know (and beyond) and keep tooting your horn.
You can’t do that with other high-reach platforms such as Reddit, and HackerNews. You are, of course, free to share the news about your product at any time, but there is no guarantee that anybody will see it (quite the opposite, actually) unless the collective mind of the community decides so, which is all but deterministic. You could easily spend a week preparing your launch post just for it to get drowned by the algorithm in minutes.
That’s why we look at Product Hunt not as the final goal (winning #1) but as simply a part of our overall launch process. It’s a great podium to be standing on, and a good excuse to talk about your product, and anything else on top is just a bonus.
We keep it simple
You will find a lot of articles (and paid courses) from “PH gurus”, explaining how you should prepare your launch months in advance, warm up your audience, prepare comments they will share, etc. We don’t do any of that. We just prepare the content (video + a few screenshots, and an intro comment), and, on the day of the launch, invite everyone we know to support us. Then, during the day, we also post on Reddit, Hackernews, and dev.to.
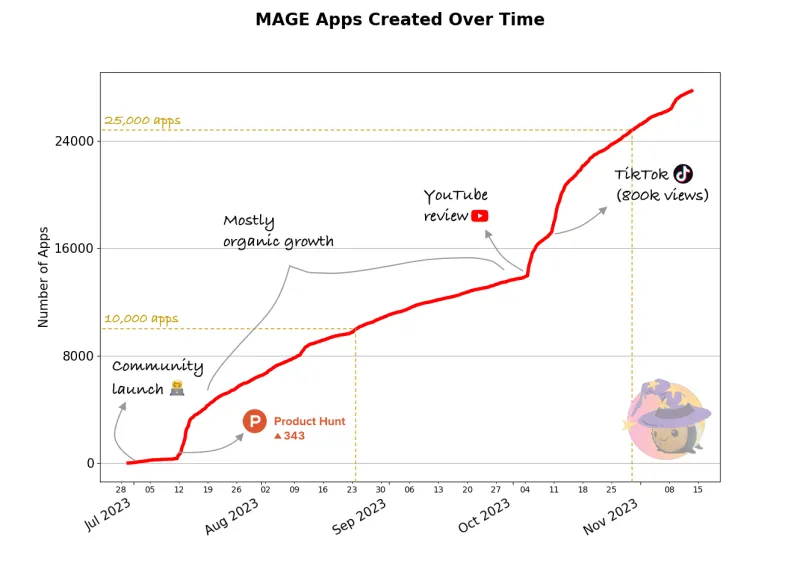
Sometimes we end up in the top 5, sometimes we don’t, but every time, we get a solid uptick in user engagement, and usually something much better follows in the next days/weeks. For example, MAGE, our GPT-powered full-stack app starter, exploded after its PH launch and has been used to create over 30,000 projects in a few months.
We do it often
Our goal is to launch on Product Hunt every 3 months as a part of our Launch Week, and that’s what we’ve done so far. You cannot really launch the exact same product unless 6 months have passed or there’s been a significant update, but you are free to launch other (sub)products and features connected to your main product.
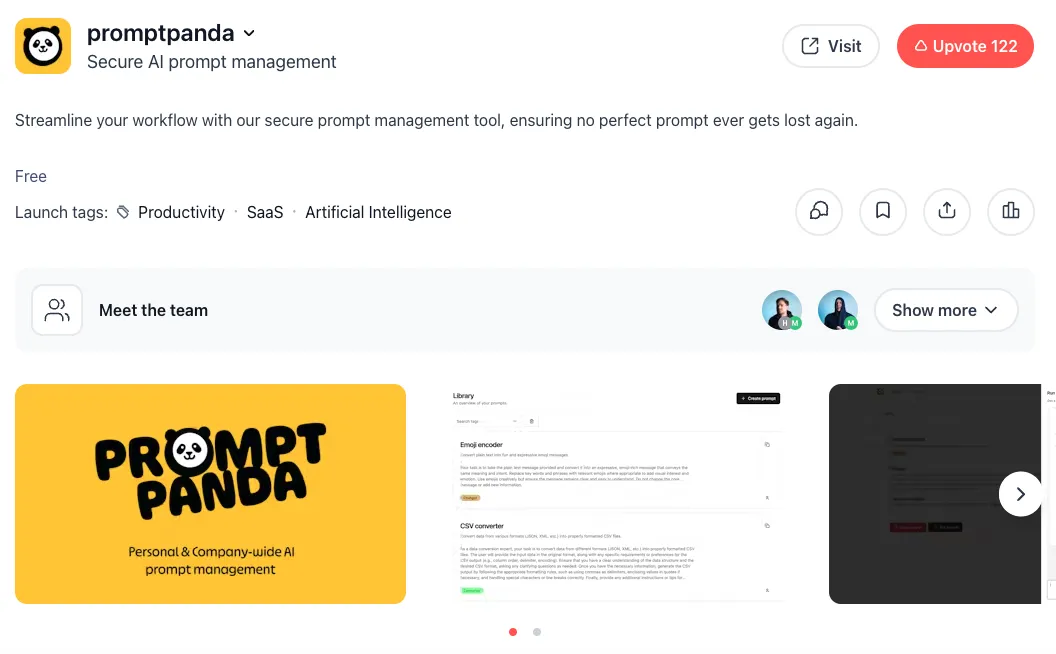
💡 Hint: when you submit a launch, you can ask the PH team to “connect” it to your product so it will appear in a list of launches for that product. Often, they do it on their own. It will look like this:
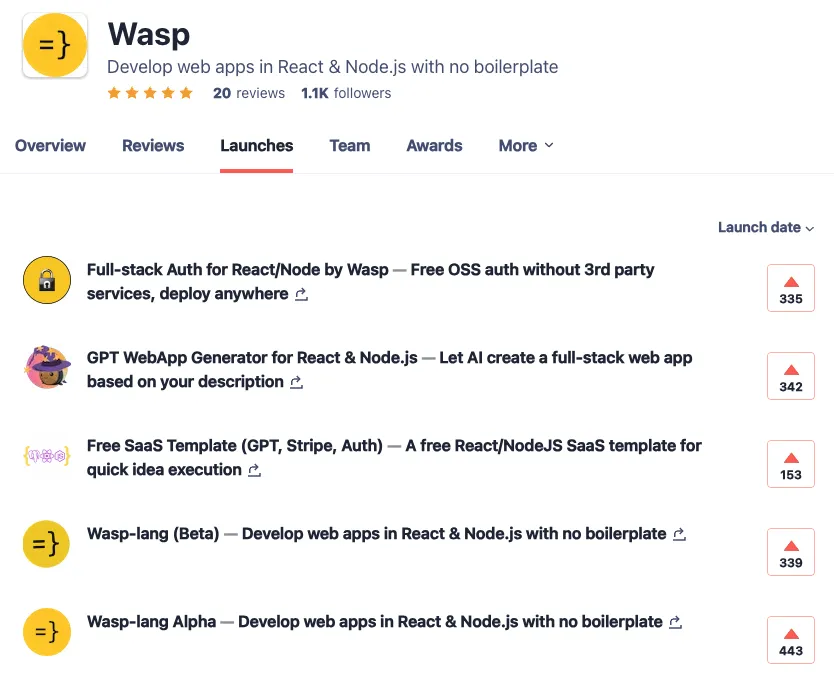
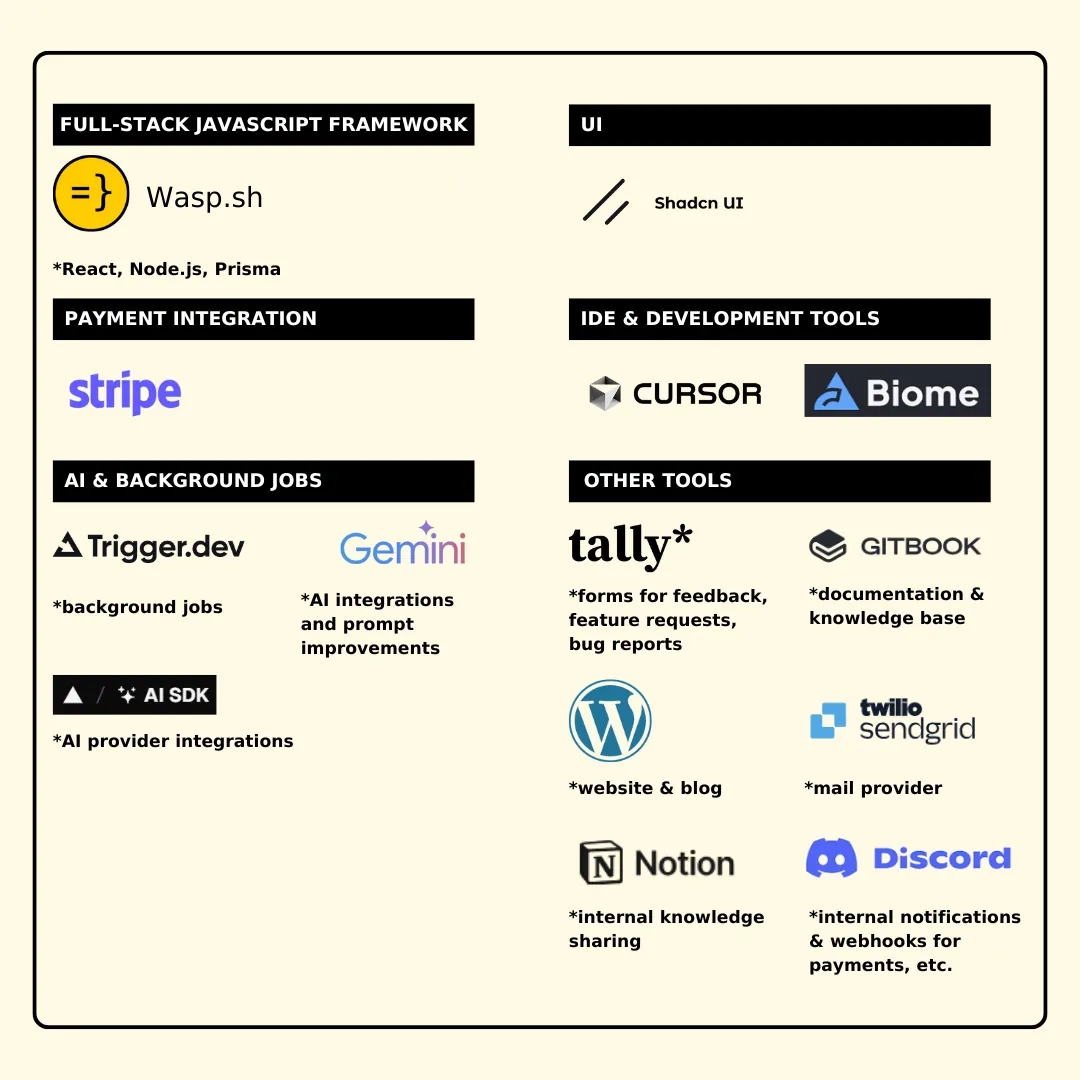
Although our main product is Wasp, a full-stack framework on top of React & Node.js, here’s what we launched so far:
- Wasp Alpha - pure product, v0 pretty much
- Wasp Beta - almost two years later, we haven’t yet adopted the “launch often” approach
- Free SaaS template - a predecessor of Open SaaS, 4 months later
- *MAGE, GPT Web App Generator* - a full-stack web app generator powered by Wasp
- Full-stack auth for React/Node, no 3rd party services - Wasp’s auth feature
- And finally, Open SaaS - A free, open-source alternative to $300+ React & Node.js SaaS starters
It’s become a regular part of our launch workflow, and for whatever new feature(s) we introduce in that quarter, we’ll look for a good candidate to showcase in the upcoming launch. That allows us to keep talking about what we do, and we also get a lot of good content (e.g., videos, banners) that we can embed in our docs, blog posts, etc.
For example, this is a video showing how auth works in Wasp - first we used it for our Product Hunt launch, and now it lives at the top of our auth docs.
Thanks for reading!
Thanks for reading this far! This turned out to be quite a bit longer post than I initially expected, but I just kept getting more ideas on what to write about. I hope you will find it helpful for planning your next launch and that you will also know a bit better what to expect along the way.
I would also love to get your feedback and hear about your experiences and strategies for launching on Product Hunt.
Happy launching!